ACCESS USB DONGLES VIA THE NETWORK
Dongle Servers by SEH
USB Dongle servers by SEH connect USB dongles securely, quickly and easily over the network. Use your copy-protected software as usual without having to plug the dongle directly into your client. By using your USB dongle over IP you can work flexibly and without any spatial limitations or restrictions due to USB cable lengths!
Versatile: use dongles across LAN, VPN, VLAN and the Internet
With the dongle servers from SEH, the dongles can not only be used via LAN network connections, but also via the VPN, VLAN and the Internet. In this way, dongles can be accessed network-wide from many types of environments. Using your USB dongle over IP results in a wide range of possible uses!
USB Dongle servers are interesting for companies
- who, as service providers, provide copy-protected software for various customers,
- are the makers of copy-protected software and
- who have many employees working remotely, in the field or operate many branch offices.
USB Dongle servers are not only an optimal solution for businesses, but also for authorities, educational institutions, research and development centers, institutions and many more!
More Freedom When Using Dongles
The "SEH UTN Manager" software tool for Windows, OS X and Linux gives you access to your dongles as if they were connected directly to your computer. The SEH UTN Manager can be installed on all notebooks, PCs, servers, and terminals that require dongle access.
Our Portfolio: The next generation of Dongle Servers

dongleserver Pro®
For small to medium-sized companies, educational and scientific institutions
The dongleserver Pro reliably and securely provides software license USB dongles over IP. The handy version of the dongle server is designed for use in office environments. Thanks to the lockable metal housing, your valuable USB dongles are kept safe in accessible environments.
Product features:
- 4 x USB 3.0 SuperSpeed Ports
- 4 x USB 2.0 Hi-Speed Ports
- Gigabit Ethernet
- for Microsoft Windows, Linux, OS X/mac OS
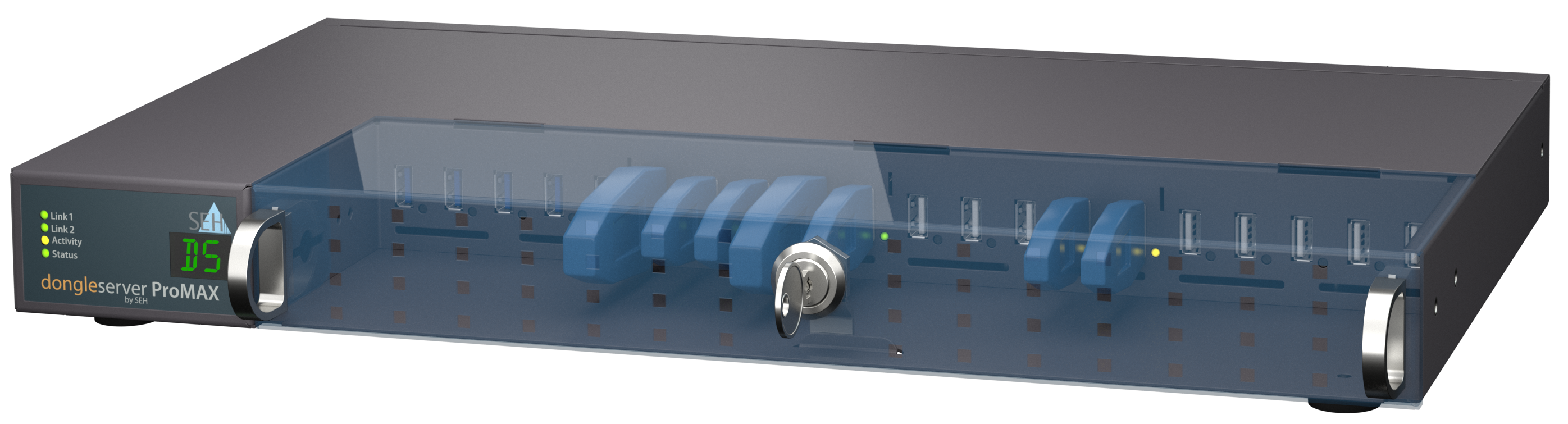
dongleserver ProMAX®
For large companies, SaaS and cloud service providers and IT systems integrators
As the large variant for server rooms or data centers, the dongleserver ProMAX provides up to 20 software license dongles over the network. Compared to the smaller dongleserver Pro, the dongleserver ProMAX offers additional reliability and redundancy with two built-in power supplies and two network connections. In addition, the parameters, passwords, and certificates are automatically backed up to an integrated SD card. The dongle server is also equipped with a multi-segment status and fault display for information at a glance.
Product Features:
- 5 x USB 3.0 SuperSpeed Ports
- 15 x USB 2.0 Hi-Speed Ports
- Gigabit Ethernet
- for Microsoft Windows, Linux, OS X/mac OS
An unbeatable duo: SEH Dongleserver & Serviceplus
Ensure additional protection and first-class support for your dongle server with our Serviceplus packages. Benefit from extended warranty periods, regular software updates and much more!
Key Features
Auto-Connect
Connections to dongles can be established automatically when the system starts, they can have a time out, or be managed in the background (without the user knowing it).
Central Analysis

All logged data is saved locally on the dongle servers and can also be sent automatically to a syslog-ng or WebDAV server for analysis.
Extensive Monitoring

Everything happening at the dongle server and its status can be monitored and logged with a date-time-stamp.
Plug & Play

Simply connect the dongle server to the network, plug in the dongles, install the software tool “SEH UTN Manager” and you're ready to go!
Security

Dongle servers come with an extensive list of security functions: Connection encryption, dongle-port-marriage, certificate management, authentication (802.1X), port access control, and much more!
Dongle-Pooling

If you have connected several identical dongles to a dongle server, the next free dongle is automatically used via the dongle pooling function.
Why do you need a Dongle Server?
- So that you never have to search for your dongles again.
- So that you never have to unplug and replug again.
- To protect your dongles against theft, damage, and loss.
- So that you can always see if someone else is currently using the dongle you need or if you can use it right now.
- So that you can easily access your dongles from anywhere in the network, even via the Internet, VPN, or VLAN.
- So that you add value to your dongles with added features: increased security, dongle user management, and much more.
- To use your dongles effectively as possible, resulting in a decrease in required licenses and lower acquisition costs.
In other words: So that your work with dongles is state-of-the-art and uncomplicated!
Dongles in Virtual Environments
SEH dongle servers are ideal for server-based environments (Citrix Virtual Apps, Microsoft Remote Desktop Services/Terminal Services) and virtualized environments (VMware, Citrix Hypervisor, Microsoft Hyper-V). The dongle server works like a virtual cable extension over the network, which you use to control the dongles and use them just as if they were connected locally.









